A breach parser is a specialized software tool designed to analyze and interpret data related to security breaches. Its primary function is to sift through vast amounts of data generated during a breach, identifying patterns, anomalies, and indicators of compromise (IOCs) that can inform cybersecurity teams about the nature and scope of the attack. By automating the process of data analysis, breach parsers enable organizations to respond more swiftly and effectively to breaches, minimizing potential damage.
In the rapidly evolving landscape of cybersecurity, the threat of data breaches has become an ever-present concern for organizations across the globe. As malicious actors continually refine their techniques to exploit vulnerabilities, the need for sophisticated tools to detect, analyze, and respond to breaches has never been more critical. Among these tools, breach parsers have emerged as a vital component in the arsenal of cybersecurity professionals. This essay aims to explore the concept of breach parsers, their functionality, and their significance in enhancing cybersecurity measures.
Moreover, breach parsers contribute to the development of more robust security measures. By analyzing data from past breaches, organizations can gain insights into the tactics, techniques, and procedures (TTPs) of adversaries. This intelligence can be used to refine threat models, strengthen vulnerabilities, and design more effective security controls.
Looking to the future, the role of breach parsers in cybersecurity is likely to grow even more significant. Advances in artificial intelligence and machine learning will enhance the capabilities of these tools, enabling them to predict and prevent breaches more effectively. Furthermore, the integration of breach parsers with other cybersecurity tools and platforms will facilitate a more holistic approach to threat detection and response.
The integration of breach parsers into cybersecurity strategies offers several significant benefits. Firstly, they enhance the speed and efficiency of breach detection and response. In the critical minutes and hours following a breach, the ability to quickly assess the situation and implement remedial actions can substantially reduce the impact of the attack. Secondly, breach parsers help in improving the accuracy of threat detection. By leveraging machine learning and pattern recognition, these tools can identify subtle indicators of compromise that might be missed by human analysts.
Despite their benefits, the deployment and effective use of breach parsers are not without challenges. One of the primary concerns is the quality and relevance of the data being analyzed. Inaccurate or incomplete data can lead to false positives or negatives, undermining the utility of the breach parser. Additionally, as cyber threats become more sophisticated, breach parsers must continually evolve to keep pace with new attack vectors and TTPs.
In conclusion, breach parsers have become an indispensable tool in the fight against cyber threats. By enabling organizations to detect, analyze, and respond to breaches more effectively, these tools play a critical role in enhancing cybersecurity. As the threat landscape continues to evolve, the development and refinement of breach parsers will be essential in protecting sensitive data and maintaining the integrity of digital systems. Through their contribution to swift and accurate threat detection, breach parsers stand as a testament to the power of technology in safeguarding our digital future.
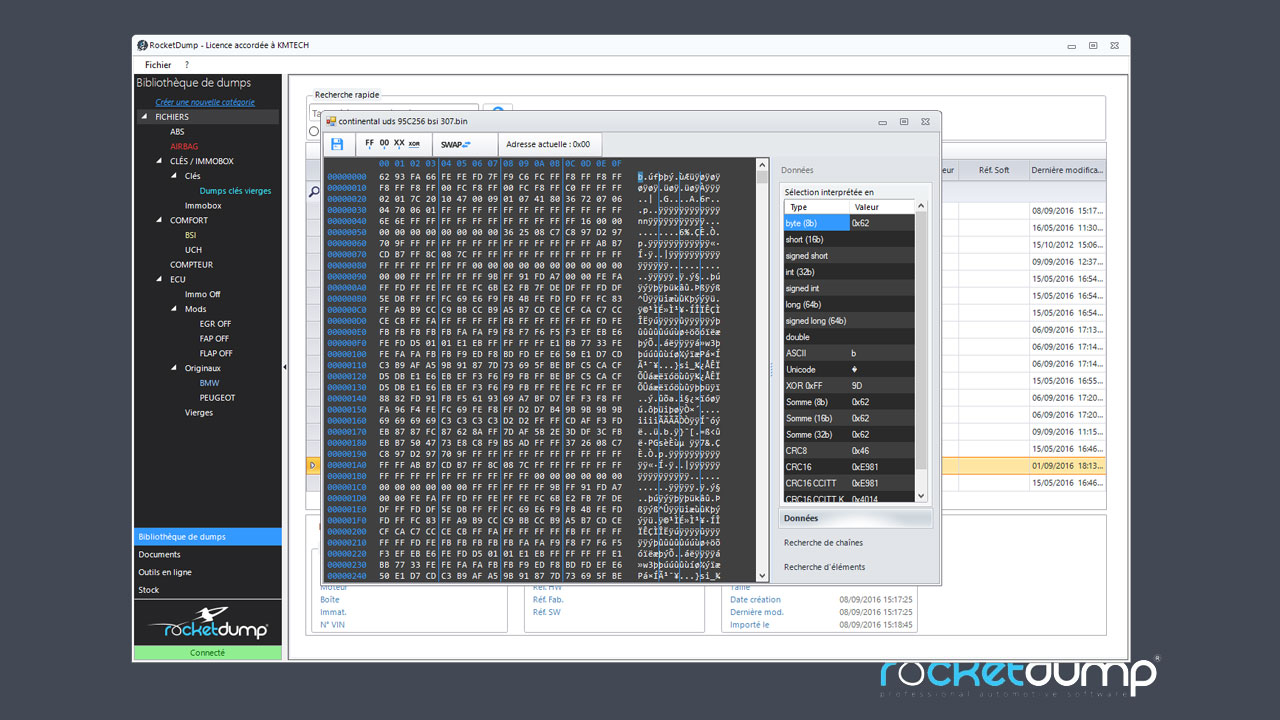
Breach parsers operate by ingesting data from various sources, including logs, network traffic captures, and threat intelligence feeds. They then apply advanced algorithms and machine learning techniques to parse this data, searching for known signatures of malicious activity, unusual behavior that may indicate a breach, and other relevant IOCs. The output of a breach parser typically includes detailed reports on the breach, such as the entry point of the attack, the methods used by the attackers, and the extent of the compromise.